Assessing Your Organization’s Cyber Security Risk with S2ORG
You’ve likely checked your personal FICO® credit score recently. Did you know there’s a similar way to assess your organization’s cyber security risk? It’s called S2ORG by SecurityStudio.
Standards like FICO® Scores allow lenders to assess risk before issuing credit. Wouldn’t it be great to be able to automate the complex task of evaluating a company’s overall cyber security and its risk of an information security incident. Our security partner SecurityStudio has developed an assessment tool called S2ORG that measures a company’s information security program on a scale from 300 (not secure) to 850 (excellent) and identifies your company’s level of vulnerabilities, gaps and deficiencies in your security program. Get an S2ORG assessment now.
1) An S2ORG Assessment is easy to understand.
Information security is a complex discipline with many moving parts, but SecurityStudio’s S2ORG process simplifies the communication about how your information security program is performing. You don’t need to be an information security expert with years of experience to understand what S2ORG is telling you. One simple number represents your overall risk, and additional indicators show where your most significant risks are.
2) S2ORG can tell you what everyone else is doing.
Hundreds of organizations have received their S2ORG score and this allows for solid, fact-based comparisons. One of the common questions we receive about information security is, “What is everybody else doing?” This question comes from the responsibility for due care/due diligence, liability, and knowing that there’s “protection in the herd.”
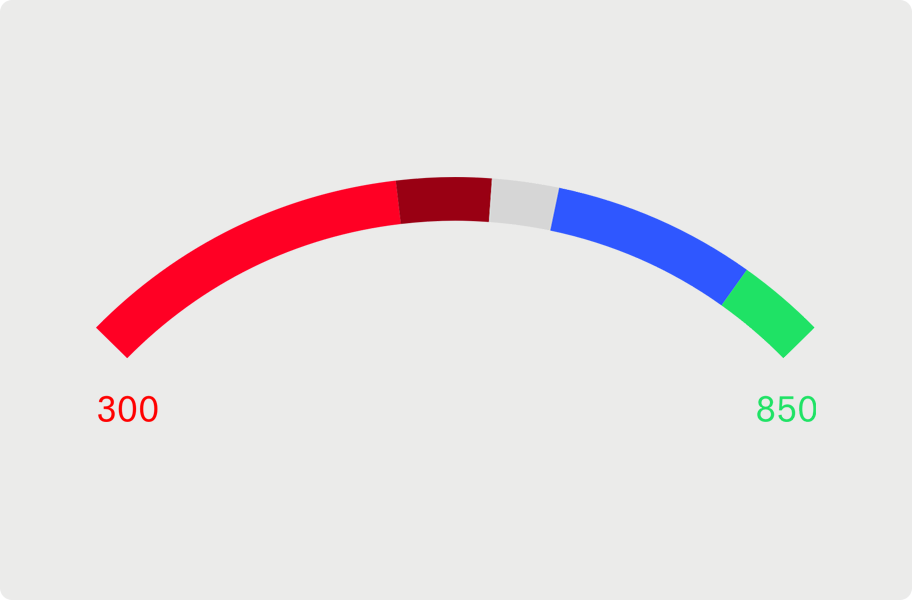
Once your full S2ORG assessment is complete, you’ll receive a risk measurement, from 300 (not secure) to 850 (excellent).
3) With S2ORG, you can track progress.
S2ORG is a point of reference that should be used to track progress and to determine whether risk is maintained within your tolerance. Your information security program and risks are always getting better or worse; they never stay the same. Questions about progress, regular reporting, and support for maintaining your information security program are all answered.
4) An S2ORG Assessment is objective.
S2ORG is maintained by an independent organization that doesn’t do consulting work, and has no other purpose but to provide accurate measurements of information security risk. In addition to organizational objectivity, the score is also objective. FISASCORE is calculated through the measurement of thousands of objective characteristics that take much of the guesswork and opinion out of the equation.
5) An S2ORG Assessment is credible.
S2ORG was developed over the course of more than 15 years through the work of seasoned information security practitioners and is now on its fifth major release. S2ORG is based on generally well-accepted information security standards. The criteria for measurement are all reference-able to the NIST Cybersecurity Framework (CSF), and its supporting standards: NIST SP 800-53, COBIT, ISO 27001:2013, and CIS CSC.

FRG offers the SecurityStudio S2Vendor module as a solution for organizations to determine how secure their vendors and partners are.
6) S2ORG represents risk.
Risk is the combination of vulnerabilities and applicable threats that manifest themselves into the likelihood of something bad happening and the impact if it did. If there is no vulnerability (or weakness) in a control, there is no risk. If there is a vulnerability in a control without an applicable threat, there is also no risk. An S2ORG measurement represents the analysis of hundreds of controls, thousands of vulnerabilities and thousands of threats, resulting in likelihoods and impacts of bad events.
7) S2ORG is comprehensive.
Fundamental to the S2ORG measurement is our definition of information security: The application of administrative, physical, and technical controls to protect the confidentiality, integrity and availability of information. There are four Phases:
Phase 1 – Administrative Controls
Phase 2 – Physical Controls
Phase 3 – Internal Technical Controls
Phase 4 – External Technical Controls
All four parts of the information security program must work well together. A weakness in one control can lead to a collapse of all others. The phases are further segmented into sections, and the sections are further segmented into controls. The final report is presented both high level and then digs deep in the details.
8) There is fast-growing community support for S2 Scores.
The partner community behind the S2 system is critical to its success. Partners work to generate S2ORG, S2VENDOR or S2TEAM scores for their clients, but the partner community is also vital to future improvements and considerations. The partner community participates in further improvements of the methodology, shares critical information, and evangelizes the need for a common information security language. Our partners include IT service companies, CPA firms, insurance brokers and security consulting companies.
9) S2ORG Scores are an indicator of future losses.
As S2ORG continues to evolve, we get closer to understanding the true losses behind information security incidents and breaches. S2ORG provides the framework for predicting future information security losses accurately, using the best information available. Today S2ORG is tied to research conducted by the Ponemon Institute for loss data.
10) Utilizing S2ORG is a competitive advantage.
Information security as a competitive advantage? Yes, absolutely! An S2ORG Assessment is a representation of the efforts you’ve put into information security and it’s a demonstration that you know where your most significant information security risks are. Armed with this information, you can make an objective case to your customers that you take information security seriously, backed by experienced information security experts, a community of partners, and a clean methodology. Don’t forget the fact that you can now invest your information security dollars where they will have the greatest benefit.
LEARN MORE:
FRG is a trusted partner providing information cyber security solutions to organizations large and small.
Wondering about how your partners’ and vendors’ S2 Scores might affect yours? Use S2Vendor to evaluate the risks presented by the providers you rely on.
Want to get a free S2ORG assessment? CLICK HERE.




